Proof of work is the mechanism that allows Bitcoin to operate without a central authority. This guide breaks down the process step by step, from hash functions to the difficulty adjustment, so beginners can understand why energy expenditure is what makes the network secure.
The Problem Proof of Work Solves
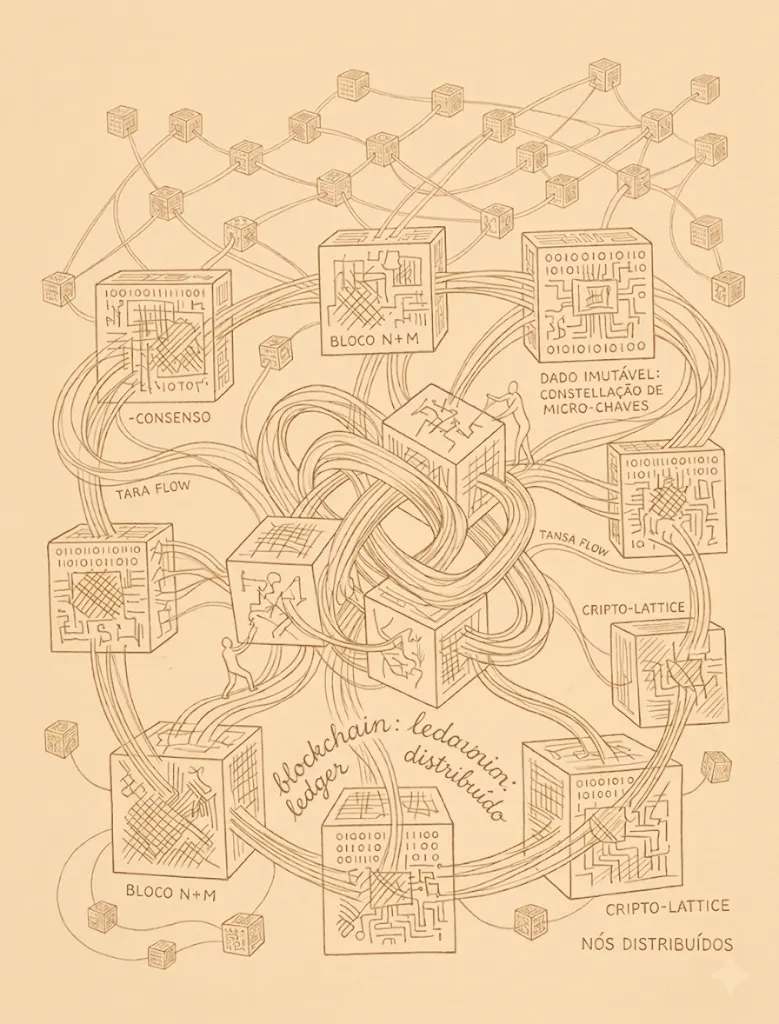
Before Bitcoin, every digital payment system relied on a trusted middleman. Banks, payment processors, and clearinghouses all served the same essential function: they kept a single, authoritative ledger and decided which transactions were valid. Remove the middleman, and you face an immediate question — if no one is in charge, who decides what happened and in what order? This is not a trivial bookkeeping detail. It is the core obstacle to building money that no single entity controls.
Proof of work is Bitcoin's answer. Rather than trusting an institution, the network trusts physics and mathematics. Participants called miners must expend real computational energy to propose a new page — called a block — for the shared ledger. That energy cost is what prevents any single actor from rewriting history or fabricating transactions. In the language of Satoshi Nakamoto's original whitepaper, proof of work establishes a system where "any needed rules and incentives can be enforced" without relying on trust. It converts electricity into digital truth.
Hash Functions: The One-Way Gate
To understand proof of work, you first need to understand hash functions. A hash function is a mathematical operation that takes any input — a sentence, a file, a block of transactions — and produces a fixed-length string of characters called a hash. Bitcoin uses SHA-256, which always outputs a 256-bit number regardless of input size. The critical property is that the process is one-way: given an input, anyone can compute the hash instantly, but given a hash, no one can reverse-engineer the original input. Even changing a single character in the input produces a completely different hash, making it impossible to predict the output without actually performing the calculation.
This one-way property is what transforms a simple math function into a security mechanism. When miners compete to add a new block, they are not solving an equation in the traditional sense. They are searching for a specific hash output by trying billions of slightly different inputs. The process is deliberately inefficient by design — and that inefficiency is the entire point. For readers who want a clear, first-principles walkthrough of how these cryptographic building blocks fit together, Yan Pritzker's *Inventing Bitcoin* is an excellent companion resource.
The Mining Process Step by Step
Here is what actually happens when a miner attempts to add a block. First, the miner gathers a batch of unconfirmed transactions from the network's waiting area, called the mempool. These transactions are assembled into a candidate block along with a reference to the previous block's hash, a timestamp, and a small arbitrary number called a nonce. The miner then feeds this entire package through SHA-256. If the resulting hash is below a specific target number set by the network, the block is valid and can be broadcast to every other node. If the hash is above the target, the miner changes the nonce and tries again — and again, and again.
Modern miners perform trillions of these hash attempts every second. The process is pure trial and error; there is no shortcut, no clever algebra that skips ahead to the answer. When a miner finally discovers a valid hash, every other node on the network can verify it almost instantly — one hash computation confirms what took trillions of attempts to find. This asymmetry between the cost of finding a solution and the ease of verifying it is the elegant heart of proof of work. The winning miner earns a block reward of newly created bitcoin plus transaction fees, which is the economic incentive that keeps the system running.
The Difficulty Adjustment: Bitcoin's Internal Thermostat
If miners keep getting faster hardware, wouldn't blocks be found too quickly? Bitcoin handles this through a mechanism called the difficulty adjustment. Every 2,016 blocks — roughly every two weeks — the protocol examines how long the previous batch of blocks took to mine. If blocks arrived faster than the ten-minute target, the difficulty increases, meaning the target hash number gets smaller and harder to hit. If blocks arrived too slowly, the difficulty decreases. This self-correcting cycle is written directly into Bitcoin's consensus rules and requires no human intervention.
The difficulty adjustment is one of the most underappreciated features of the protocol. It ensures that no matter how much computing power joins or leaves the network, new blocks continue to arrive at a predictable pace. This predictability is what makes Bitcoin's fixed supply schedule credible: roughly every four years, the block reward is cut in half, and the difficulty adjustment guarantees that miners cannot accelerate the issuance by simply adding more machines. The rules are enforced by code that every node independently verifies, a concept closely related to why self-custody matters — you verify, rather than trust.
Why Energy Expenditure Is a Feature, Not a Bug
Critics often point to Bitcoin's energy consumption as wasteful. From a first-principles perspective, however, the energy is precisely what gives the ledger its integrity. To rewrite even a single confirmed block, an attacker would need to redo all the proof of work for that block and every block that came after it, faster than the rest of the network continues to extend the chain. The deeper a transaction is buried under subsequent blocks, the more energy an attacker would need to expend — energy that has already been irreversibly consumed by honest miners. This is what makes confirmed Bitcoin transactions practically irreversible.
Think of it this way: the accumulated energy in the blockchain is a physical wall protecting every transaction behind it. No amount of clever software or political influence can substitute for the raw thermodynamic cost already paid. This is a fundamentally different security model than traditional finance, where a database administrator or court order can reverse entries. Hal Finney, one of the earliest contributors to Bitcoin, recognized this immediately — the system's security comes not from authority but from the laws of physics applied through computation.
What Proof of Work Means for You
If you are new to Bitcoin, proof of work is the reason you can trust the network without trusting any particular person or company. Every ten minutes, miners around the world compete to extend a ledger that no single government, corporation, or individual controls. The rules are open-source, verifiable in the Bitcoin Core codebase, and enforced by tens of thousands of independent nodes. When you receive bitcoin and see confirmations accumulating, each confirmation represents another layer of real-world energy securing your transaction. Understanding this process transforms Bitcoin from a mysterious buzzword into a comprehensible system grounded in mathematics and physics.
Proof of work is not the only consensus mechanism in the broader cryptocurrency landscape, but it is the one that underpins Bitcoin's specific security guarantees and monetary policy. For those who want to go deeper, the Bitcoin education resources on this site explore related topics like self-custody, node operation, and the history of the protocol. The journey from slogan to understanding is shorter than most people expect — and it begins with appreciating that behind every block is a real expenditure of energy, converting the physical world into an incorruptible digital record. This editorial discipline helps readers connect the monetary rule to the practical decisions they will make as they continue learning.